BE Computer (2012 Course)
Semester-2, Elective-4(a) Feb 2017
Software Design methodologies and Testing
Time: 1 hour Marks: 30
Q1) a) Explain 4+1 architecture view. (4 marks)
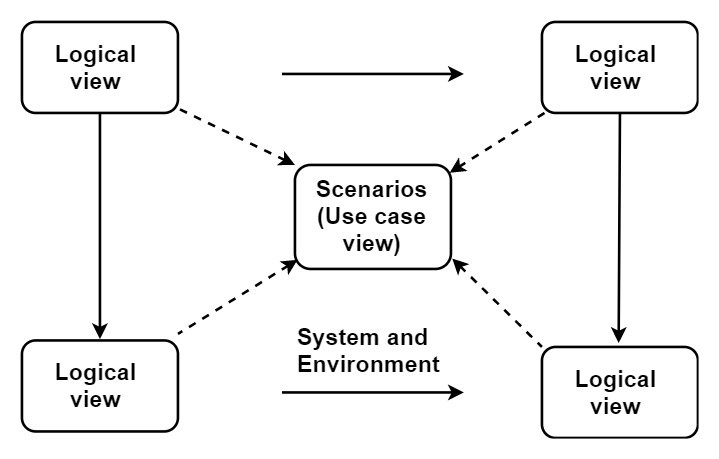
Fig. 4+1 architecture view
- Logical view: It is related to functionalities offered to end user of a system. The module can be represented by sequence, class and communication diagram.
- Development view: It is also called as component design view. This is the developer’s view who contributes to project development. The module can be represented by component and package diagram.
- Process view: It is related to runtime aspects of the system which describe program structure at runtime. It also deals with concurrency, performance, and scalability.
A module can be represented by activity diagram.
- Physical view: It is system engineer point of view and related to deployment, administration, and environment of the system. This view represents tools and its interaction, supporting software. The module can be represented by deployment diagram.
- Scenarios: Scenario at the center represents the fifth view which refers as use case view.
Q1) b) What is extends and include stereotype in use case diagram? Draw a use case diagram for ATM system. (6 marks)
Let discuss extend first:
Extend:
- Use case which represents extended functionality is called as extended use case. For representing a precise location in the base use case, an extension point is used.
- Extension occurs when some part of use case is optional and it is required to show the different functionality of the system.
- Also, when the particular condition happens and at that time if you want to display the sub-flow of the system then an extension can occur.

Fig. Use case for extend relationship
- Through mark attendance, two extensions are created mark online attendance and mark OTA attendance. Here base use case is update lecture details.
Include:
- Any other use case can use the functionality of include use case. A different use case can include the same functionality by extending it to inclusion use case.
- For an employee, at the time of filling their personal information which will store as employee record, their mobile number is validated with the help of OTP. The id-card use case is also generated for id cards. If employee lost its id- card then he can use its mobile number for making duplicate id card. Here we can include Validate-using-OTP into employee-records and id-generation.

Fig. Inclusion relationship
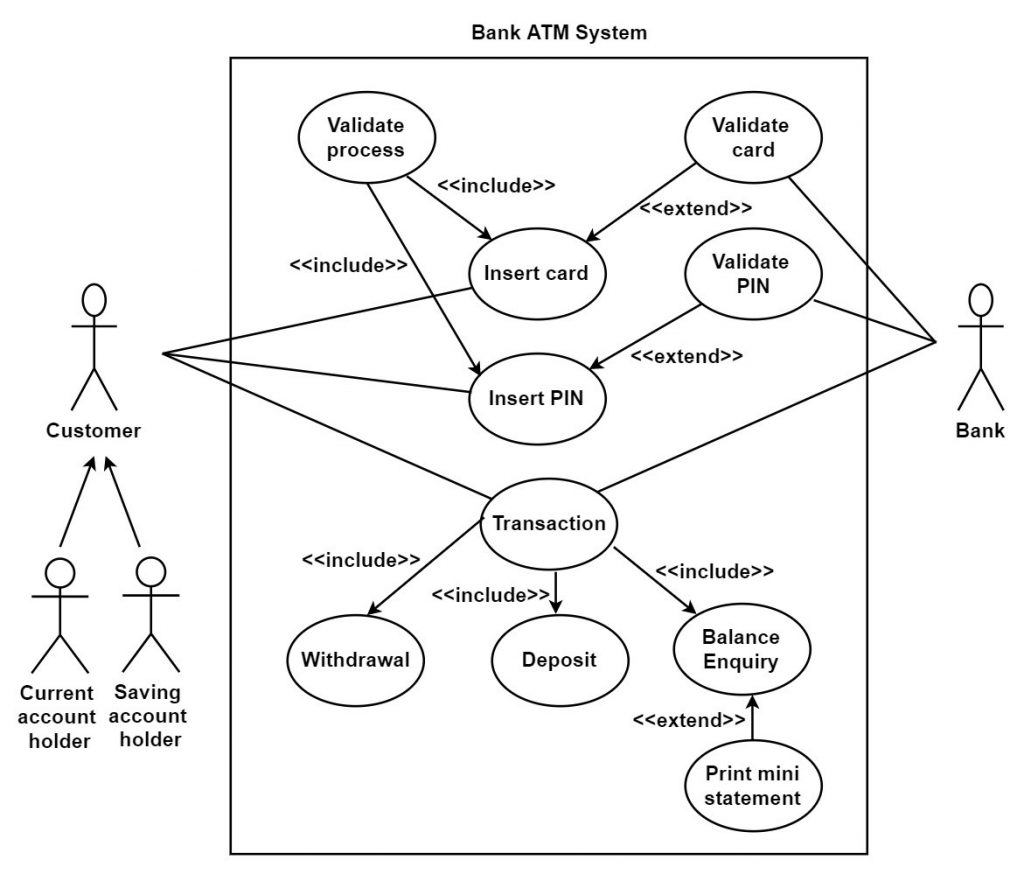
Fig. Use case diagram for ATM system
Q2) a) Explain aggregation, composition, and generalization with reference to the class diagram. (6 marks)
Generalization:
- Generalization is used to show the parent-child relationship.
- A child can have its own additional attributes and operations but it makes use of parent’s attributes and operations.
- Generalization means the child is substitutable for a declaration of the parent. Child overrides the implementation of the parent.
- Let take an example, a parent may define display method for displaying some message while child triangle may use same method name display to display the area of the triangle. This overall mechanism of overriding the operation is also known as polymorphism.
- It is also called as “is-a-kind-of” relationship.
- Generalization is represented by a solid line with an unfilled triangular arrowhead.

Fig. Generalization
Aggregation and composition:
- Both represent whole part of the relationship.
- The composition is more restricted than aggregation.
- Aggregation does not contain restriction and the presence of a contained object is optional in aggregation.
- Example: We take the example of book library which contains books and students and both share aggregate relationship but books and library share composition relationship. A library is not possible without books.
Q2) b) Differentiate between static and dynamic modeling with an example. (4 marks)
| Sr. No. | Static Modeling | Dynamic modeling |
| 1 | It represents static and structural components. | It represents behavioral components. |
| 2 | It is time independent. | It is time dependent. |
| 3 | It is also known as structural modeling. | It is also known as behavioral modeling. |
| 4 | In this, class and object diagrams are drawn. | In this, activity, sequence, state diagrams are drawn. |
Q3) a) Explain client-server software architecture. Describe multiple client/multiple service architectural patterns with the example. (6 marks)
Client-server architecture:
- In this, client act as requester and server act as a provider for service. A client may require database service or file service etc.
- The server is a combination of software and hardware that host service while service is an application specific functionality.
- Multithreading is used in the server for creating multiple threads for successfully handling of the client request. After serving the request, threads are immediately destroyed. The server can execute one service or multiple services.
- There are three client-server architecture patterns they are:
- Multiple clients and single service.
- Multiple clients and multiple services.
- Multi-tier client service.
Multiple client/multiple service architectural pattern:
- In this, multiple clients can send a request to multiple servers which host the services and servers can communicate with each other to synchronize their operation or to take required service from another server.
- For multiple clients, there are multiple servers/services available therefore it is named as multiple clients multiple service/server.
- The client can communicate with each service concurrently.

Fig. Multiple clients multiple service architecture
- Here, we take the example of banks. Banks have their multiple ATM centers. Suppose, the client has its account in two banks then he can access the service of the first bank from its ATM as well as from the ATM of the second bank and vice versa. Thus, the client can access the multiple services of the same bank as well as from different bank ATM centers.
Q3) b) Explain hierarchical control architectural pattern in real time software architecture. (4 marks)
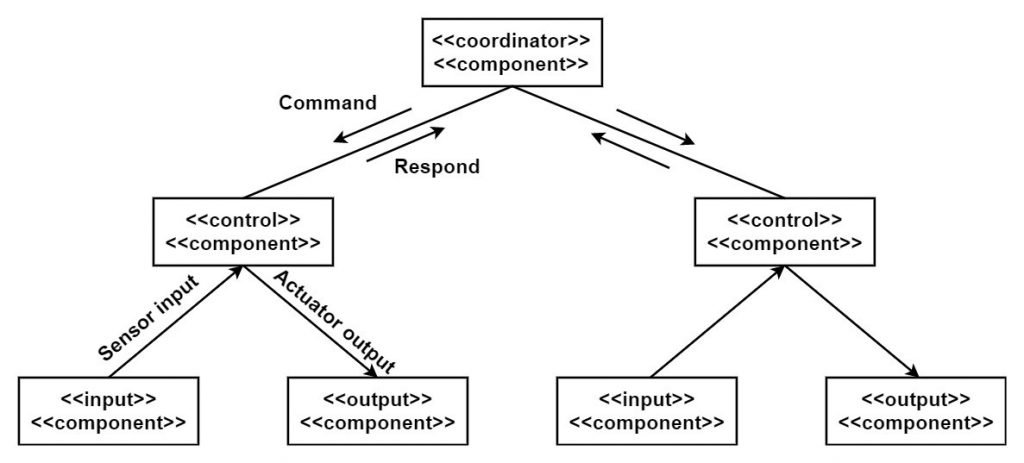
Fig. Hierarchical control architectural pattern
- It is also called as multilevel control pattern.
- As shown in architecture, coordinator components control all controlling components. Several components are present and each control components control the part of the system.
- For every controlling component, coordinator components decide the task and get the status information from all controlling components periodically.
Q4) a) Explain port, provided interface and required interface with an example. (6 marks)
Port:
- It is used for connection of two components through interfaces.
- It is a physical entity.

Fig. Port
Provided Interface:
- It specifies the operation that components must fulfill.
- It represents the formal contract of service that user gets.
- Letter P is used to represents provided a port.
Fig. Provided interface
Required interface:
- It describes the operation which is provided by another component for operating properly in the specific environment.
- Letter R used to represent required port while letter I is used to represent interface.
- Required and provided interface is linked to internal service by require and provided ports.

Fig. Required interface
Q4) b) Explain service discovery pattern in SOA. (4 marks)
Ans: coming soon
Q5) a) Explain intention, motivation, and participants of factory pattern with an example. (6 marks)
Intention:
It used to create an object without displaying creation logic to a user and provide a way for referring newly created objects through a common interface.
Motivation:
It is used by C#, C++, Java languages. It is most commonly used design pattern. The variations in factory pattern are factory method and abstract factory.
Participants:
- When a client requires a product then it does not create it by using new operator instead of it request for dedicated factory object for the product and declare which type of object he needs to the factory.
- Now factory creates the new product and gives it to the client. The client can use this new product as an abstract product since it is casted from abstract product class.
- The client is not aware of internal implementation.
- As shown in the figure, a factory class offers create product () method which returns abstract product reference.
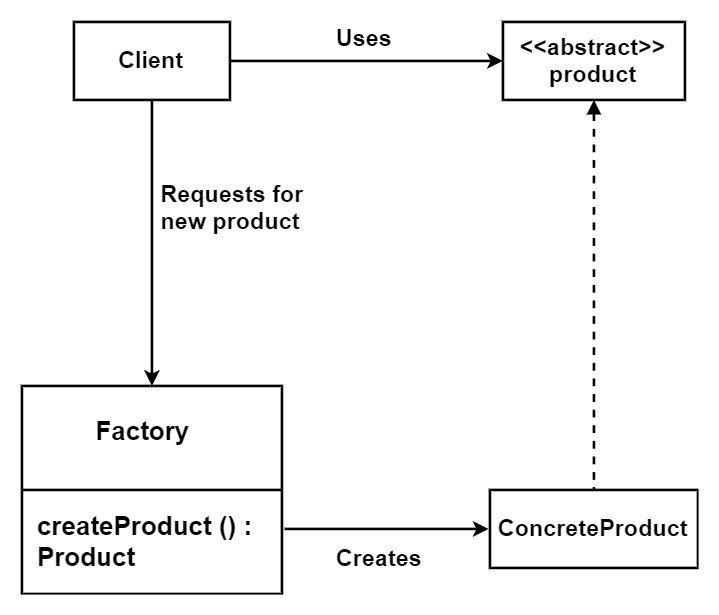
Fig. Implementation of factory pattern
Q5) b) Describe singleton pattern and its significance with an example. (4 marks)
- In singleton pattern, only one instance of the class must be created and which can be used as a global point of access. In this, the class is responsible for instantiating itself.
- In this, a class ensures that only one instance of a class exists by keep tracking itself. Thus, a special operation allows the user to access the unique instance.
- There is no any collaboration of classes for accessing the singleton instance. User access the instance from the well-defined access point.
- If any other instance is present and class gets a request to instantiate itself again then it rejects the request.
- It makes the system free from global variables.
- Singleton class is supposed to encapsulate its sole instance.
- For example, there should be only one instance of antivirus scan is running in a system.
Q6) Write short notes (Any two): (10 marks)
- Iterator pattern.
- Proxy pattern.
- Observer services.
Iterator pattern
- Characteristic:
- The client can iterate through objects without showing the internal architecture of aggregate object.
- We can iterate objects in many ways depending on application requirements.
- It is also called as cursor pattern.
- We can access the elements of an aggregate object sequentially.
- Consequences:
- It provides an easy interface to the aggregate object.
- We can traverse the elements of the aggregate object. According to requirements of application and type of data structure, the traversal mechanism is decided.
- Some condition allows more than one traversal on the aggregate object.
- Applications:
- We can use iterator pattern in library management system.
- Iterator design pattern is also used in Java and .net programming.
Proxy pattern:
- It is used to provide the placeholder for another object to control access to it.
- It can provide an interface to file, network connection etc.
- In some cases, care should be taken that costly objects should not be fully initialized. They contain objects of high preference which acquire more resources.
- Those few methods can initialize by the proxy lightweight object.
- For example, when we open gallery application on our phone, images should be listed according to the folder and all the images do not need to be loaded at first.
- When the user enters into the folder then images are rendered by the application. After fully loaded, more operations can be performed on images.
- Thus, when we open our gallery, proxy object responds with limited information about images. High-resolution images can be loaded and rendered at next stages.
Observer services:
- Characteristic:
- In this, when a state of one object changes, all dependent objects are automatically updated.
- Notify operation of observers get called when the object has to be notified about the state change occur.
- In this, one object is considered as a subject which maintains the record of observers.
- Concrete subject stores the states which need to be observed by observers.
- Concrete Observer maintains a reference to concrete subject object.
- Consequences:
- Notifications are broadcasted to all objects who subscribed for state change event.
- If subject state change depends on another object state then, in that case, subject play the role of observer and other object becomes subject. In this manner, the updates and notifications can be cascaded to different levels of observers and subject.
- The subject does not have the knowledge of the concrete class of observer which can cause loose coupling between observer and subject.
Applications:
- In Computer network monitoring system, monitoring system act as observer pattern.